What Is A Sleeper Agent? The Hidden Threat Behind Operational Secrecy
What Is A Sleeper Agent? The Hidden Threat Behind Operational Secrecy
A sleeper agent represents one of the most insidious covert threats in modern intelligence operations—an entrant designed to remain dormant until activated, blending seamlessly into society while pouncing when least anticipated. Operating under layers of secrecy, these agents infiltrate institutions, governments, and military structures with the goal of sabotage, espionage, or systemic disruption without immediate detection. Unlike conventional spies, sleeper agents do not announce their presence; instead, they “sleep” for years or even decades, emerging only when operational timing aligns with strategic advantage.
This hidden nature makes them exceptionally dangerous, challenging counterintelligence efforts and undermining national security from within.
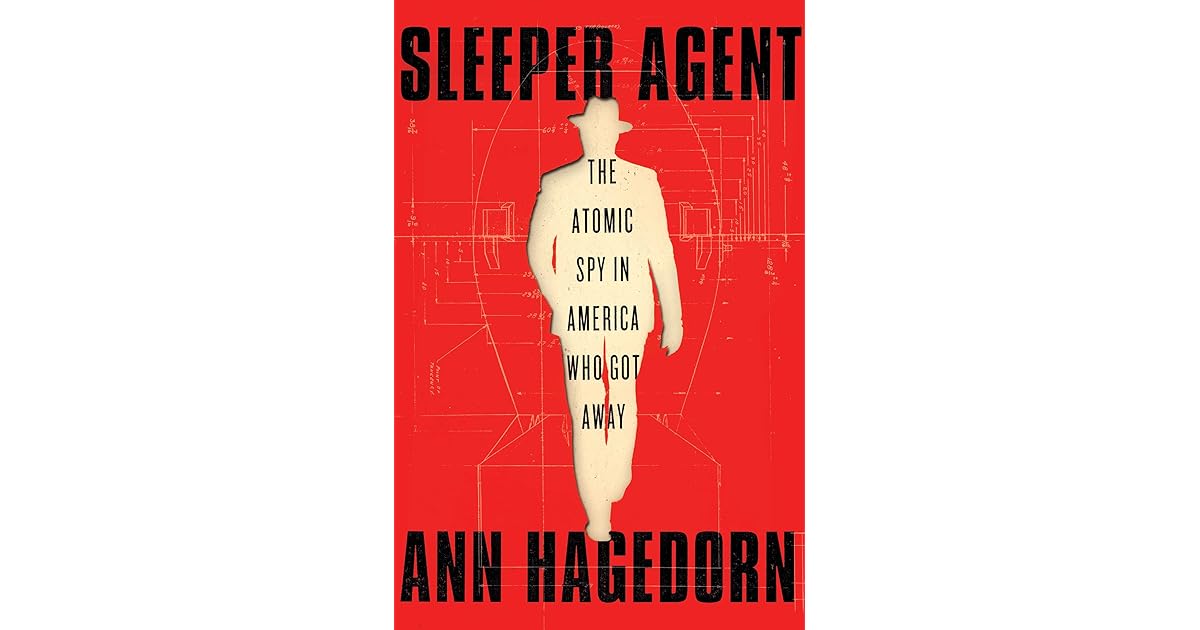
Sleeper agents operate on a principle far more alarming than mere surveillance or inquiry—they are cells of deception cloaked in normalcy. The term “sleeper” itself underscores their modus operandi: initial latency followed by sudden activation. Historically, developmental models of such agents date back to Cold War intelligence strategies, where Soviet and Western agencies alike explored psychological manipulation and identity infiltration.These operatives are often cultivated over time, trained in multiple personas, languages, and survival tactics, enabling them to disappear into civilian life. Once triggered—by a coded signal, geopolitical shift, or personal loss—recovered sleeper agents launch coordinated attacks that exploit vulnerabilities too deeply embedded for traditional defenses to counter quickly.
Central to the threat lies operational secrecy, which allows sleeper agents to remain untraceable for extended durations.
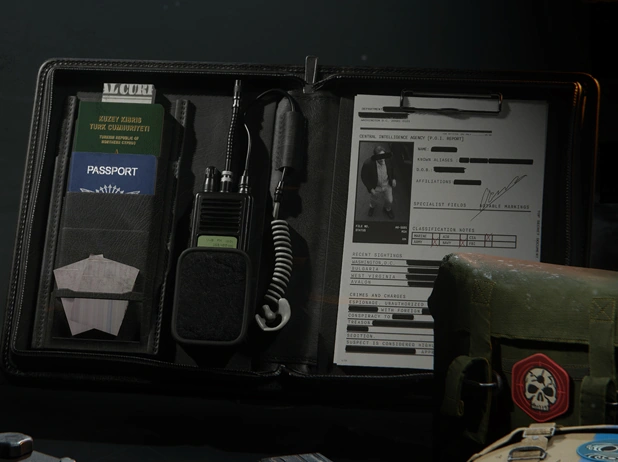
The invisibility they achieve stems not from invisibility technology, but from institutional camouflage: assuming everyday identities, holding jobs, forming relationships, and building social standing under strict operational discipline. This camouflage is not passive. It requires meticulous planning and psychological resilience. Recruitment often targets individuals with access, emotional stability, psychological resilience, and a propensity for compartmentalization—traits that enable seamless role-shifting without cognitive rupture.
Once embedded, sleeper agents may spend years not whistleblowing, but silently observing, gathering intelligence, and preparing activation triggers.
The success of such operations hinges on the absence of counterintelligence breakthroughs—intelligence cultures that fail to detect subtle behavioral anomalies or connections across datasets. Operational secrecy becomes both weapon and shield: hiding intent beneath layers of routine, severing digital and social traces long enough to cross critical thresholds.
Historical examples illuminate the systemic danger—from the Cambridge Five to modern cyber infiltration networks.
The Cambridge Five, a notorious ring of Soviet sleeper operatives embedded in Britain’s creation and leadership during the 1930s and 1940s, exemplify how deep infiltration can compromise national security for decades.Their unmasking in the 1950s exposed vulnerabilities in vetting protocols and the catastrophic lag between infiltration and detection. Today, sleeper agent threats extend beyond espionage into hybrid warfare: sleeper cells now train in cyber sabotage, disinformation networks, and critical infrastructure infiltration, blurring lines between foreign intelligence and asymmetric attack vectors. The real challenge lies in detection.
Traditional surveillance struggles to identify agents whose actions appear below alert thresholds.
Counterintelligence relies heavily on behavioral analysis, cross-agency data fusion, and long-term monitoring—efforts hampered by bureaucratic silos and information hoarding.
Yet recent advances in behavioral profiling, biometric tracking, and network analysis offer new tools. Intelligence communities increasingly emphasize metadata correlation, psychological resilience testing, and early-warning systems to disrupt sleeper recruitment before activation.The evolution of sleeper threats demands equally adaptive countermeasures rooted in intelligence integration rather than fragmented analysis. Operational secrecy, while vital for national defense, paradoxically empowers sleeper agents by shielding their early stages. But awareness is growing: governments now invest in “ распол anterior defense,” training personnel to detect subtle inconsistencies—delayed recall, emotional detachment, unexplained loyalties—that once appeared innocuous.
The rise of AI-assisted anomaly detection adds urgency, minimizing human blind spots, though ethical concerns about surveillance overreach persist. Sleeper agents symbolize a hidden war fought not with weapons, but with identity and time. Their existence challenges fundamental assumptions about trust, transparency, and institutional resilience.
As global security landscapes shift, securing society against these unseen threats demands not only technical sophistication but cultural vigilance—an imperative that turns operational secrecy into a line of defense rather than a vulnerability. The vigilance required to uncover and counter sleeper agents is as much a psychological and procedural battle as it is a technical one, defining the next frontier in national security.


Related Post

How Many Children Does Frankie Avalon Have? Unveiling the Legacies Behind the Sultry Serviceman

Film The Final: The Silent Revolution Shaping Cinema’s Final Moment
Mary Anne Den Bok: Pioneering Authenticity in Personal Branding and Women’s Leadership

Ashton Meem: From Height, Age, and Strength — Unpacking His Bio, Net Worth, and Single Facts

